
Yisaitong Electronic Document Security Management System is a professional data security management software designed to help users protect the security of their electronic documents. . It provides a series of functions and tools that enable users to easily manage and control access to their electronic documents to prevent unauthorized access and leakage.
Yisaitong is a company specializing in document security, data security and network security services. Our company uses the system of Yisaitong, especially its document encryption system, which has high security and complete functions, which can effectively protect the security of computer files and document data.
First, after logging in to the Yisaitong electronic document, enter my interface, and then click to enter the setting interface. Secondly, click the security management system and opt out of the current security management system. In addition, the electronic documents of Yisaitong, which are withdrawn from the security management system, will be weakened from the perspective of security. Pay attention to privacy protection.
Document security products jointly created by Yisaitong and Green League Cloud, Alibaba Cloud and Huawei Cloud: document security management system, document transparency and decryption system, DLP data leakage protection solution and many technologies.
1. System file refers to the folder that stores the main files of the operating system. Generally, the relevant files are automatically created and placed in the corresponding folder during the installation of the operating system, and the files in it directly affect The normal operation of the system is not allowed to be changed at will. Its existence plays an important role in maintaining the stability of the computer system.
2. File management system is a computer software used to organize and manage digital data files, including text documents, images, audio and video and other types of files.
3. File system: refers to the file management system in the computer operating system, which is essentially a software system for managing and accessing files. It is composed of files and management programs.File system function: It can define the required file organization and provide an environment for establishing and accessing data.

1. First of all, you may as well check the available Information of hard drive and LVM roll. The following command will display information about existing disk storage devices, storage pools, LVM volumes and storage snapshots.The output comes from the newly installed CentOS 7, which uses LVM and XFS file systems by default.
2. Asynchronous processing. When modifying, read the file into the memory and mark it as clean. After modification, it is marked as dirty but not immediately written to the hard disk, and sync needs to be called. Abnormal shutdown will lead to disk verification.
3. After creating a file system for the partition, the next step is to mount it to a mount point under the virtual directory, so that the data can be stored in the new file system. You can mount the new file system to any location in the virtual directory that requires additional space through the mount command.
Global trade metadata enrichment-APP, download it now, new users will receive a novice gift pack.
Yisaitong Electronic Document Security Management System is a professional data security management software designed to help users protect the security of their electronic documents. . It provides a series of functions and tools that enable users to easily manage and control access to their electronic documents to prevent unauthorized access and leakage.
Yisaitong is a company specializing in document security, data security and network security services. Our company uses the system of Yisaitong, especially its document encryption system, which has high security and complete functions, which can effectively protect the security of computer files and document data.
First, after logging in to the Yisaitong electronic document, enter my interface, and then click to enter the setting interface. Secondly, click the security management system and opt out of the current security management system. In addition, the electronic documents of Yisaitong, which are withdrawn from the security management system, will be weakened from the perspective of security. Pay attention to privacy protection.
Document security products jointly created by Yisaitong and Green League Cloud, Alibaba Cloud and Huawei Cloud: document security management system, document transparency and decryption system, DLP data leakage protection solution and many technologies.
1. System file refers to the folder that stores the main files of the operating system. Generally, the relevant files are automatically created and placed in the corresponding folder during the installation of the operating system, and the files in it directly affect The normal operation of the system is not allowed to be changed at will. Its existence plays an important role in maintaining the stability of the computer system.
2. File management system is a computer software used to organize and manage digital data files, including text documents, images, audio and video and other types of files.
3. File system: refers to the file management system in the computer operating system, which is essentially a software system for managing and accessing files. It is composed of files and management programs.File system function: It can define the required file organization and provide an environment for establishing and accessing data.

1. First of all, you may as well check the available Information of hard drive and LVM roll. The following command will display information about existing disk storage devices, storage pools, LVM volumes and storage snapshots.The output comes from the newly installed CentOS 7, which uses LVM and XFS file systems by default.
2. Asynchronous processing. When modifying, read the file into the memory and mark it as clean. After modification, it is marked as dirty but not immediately written to the hard disk, and sync needs to be called. Abnormal shutdown will lead to disk verification.
3. After creating a file system for the partition, the next step is to mount it to a mount point under the virtual directory, so that the data can be stored in the new file system. You can mount the new file system to any location in the virtual directory that requires additional space through the mount command.
HS code-based data mining for analytics
author: 2024-12-24 02:56Cross-border HS code harmonization
author: 2024-12-24 02:54Steel pipes (HS code ) trade insights
author: 2024-12-24 01:48Renewable energy equipment HS code mapping
author: 2024-12-24 01:08End-to-end supplier lifecycle management
author: 2024-12-24 02:56HS code-driven customs clearance SLAs
author: 2024-12-24 02:50HS code-driven supplier rationalization
author: 2024-12-24 02:48Real-time cargo utilization metrics
author: 2024-12-24 02:43Organic chemicals (HS code ) patterns
author: 2024-12-24 02:23 Maritime logistics HS code mapping
Maritime logistics HS code mapping
261.28MB
Check How to leverage global trade intelligence
How to leverage global trade intelligence
665.68MB
Check Dynamic supplier inventory analysis
Dynamic supplier inventory analysis
854.42MB
Check HS code indexing for procurement catalogs
HS code indexing for procurement catalogs
628.38MB
Check How to analyze customs transaction records
How to analyze customs transaction records
341.94MB
Check Asia trade analytics platform
Asia trade analytics platform
658.83MB
Check HS code integration with digital customs forms
HS code integration with digital customs forms
765.92MB
Check Commodity price indexing by HS code
Commodity price indexing by HS code
255.26MB
Check Timber (HS code ) import patterns
Timber (HS code ) import patterns
335.82MB
Check HS code verification for exporters
HS code verification for exporters
885.44MB
Check Pharma R&D materials HS code verification
Pharma R&D materials HS code verification
467.18MB
Check How to use trade data for pricing strategy
How to use trade data for pricing strategy
846.18MB
Check Granular HS code detail for compliance officers
Granular HS code detail for compliance officers
392.98MB
Check Predictive analytics for trade flows
Predictive analytics for trade flows
543.83MB
Check Commodity price indexing by HS code
Commodity price indexing by HS code
734.18MB
Check Value-added exports by HS code
Value-added exports by HS code
248.57MB
Check HS code metrics for performance dashboards
HS code metrics for performance dashboards
354.73MB
Check Real-time supply-demand matching
Real-time supply-demand matching
284.27MB
Check Trade data for construction materials
Trade data for construction materials
677.13MB
Check international suppliers data
international suppliers data
213.69MB
Check Customs duty prediction models
Customs duty prediction models
961.85MB
Check Canada HS code classification assistance
Canada HS code classification assistance
319.74MB
Check How to align trade data with marketing
How to align trade data with marketing
325.92MB
Check How to find reliable global suppliers
How to find reliable global suppliers
282.78MB
Check HS code-driven cross-border e-commerce
HS code-driven cross-border e-commerce
469.62MB
Check Commodity price indexing by HS code
Commodity price indexing by HS code
341.24MB
Check Global supply chain security insights
Global supply chain security insights
776.76MB
Check Supply contracts referencing HS codes
Supply contracts referencing HS codes
273.51MB
Check Top supply chain intelligence providers
Top supply chain intelligence providers
886.74MB
Check Shipping lane performance metrics
Shipping lane performance metrics
637.85MB
Check Global HS code repository access
Global HS code repository access
217.27MB
Check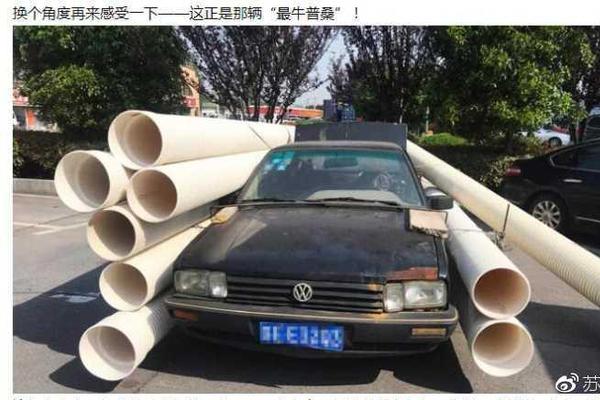 Global trade data for PESTEL analysis
Global trade data for PESTEL analysis
115.11MB
Check Customs data verification services
Customs data verification services
661.56MB
Check How to access restricted trade data
How to access restricted trade data
512.15MB
Check Import export cost optimization
Import export cost optimization
843.91MB
Check How to secure competitive freight rates
How to secure competitive freight rates
733.51MB
Check
Scan to install
Global trade metadata enrichment to discover more
Netizen comments More
926 Comparative trade performance metrics
2024-12-24 03:15 recommend
1276 How to leverage customs rulings data
2024-12-24 02:23 recommend
625 Global trade data-driven forecasting
2024-12-24 02:05 recommend
2763 Predictive trade infrastructure analysis
2024-12-24 01:42 recommend
727 Trade data for construction materials
2024-12-24 01:00 recommend